Multiple groups of state-sponsored hackers are currently attacking a recently discovered vulnerability in Microsoft Exchange servers.
The attacks were first detected by Volexity, a British cyber-security firm. At the start of the week they were also confirmed to ZDNet by a source at the US Department of Defense. According to the DOD source, “all the big players” have been exploiting the vulnerability since a Microsoft patch on Tuesday, February 11. In IT circles, the resulting vulnerability is being tracked using the identifier CVE-2020-0688.
Not long after further details about the bug were revealed by the Zero-Day Initiative on February 26th, three proof-of-concept exploits had already found their way to GitHub, and a Metasploit module wasn’t far behind. In the meanwhile, the respective APT groups (advanced persistent threats) have been targeting this vulnerability on servers which have not yet been secured with a patch provided by Microsoft. Of course, such attacks are not so easily carried out, as the hackers require at least one set of credentials for an email account on the Exchange server to exploit the bug – something that amateur hackers, also known as script kiddies, usually don’t have access to. Unfortunately, credentials of accounts that are additionally protected by 2-factor authentication can also be used to exploit the vulnerability – without first having to bypass 2FA …
Exchange has become the predominant email server at companies. The current spate of attacks places practically all versions at risk (apart from Exchange Online included in Office 365, for which Microsoft installs its own patches).
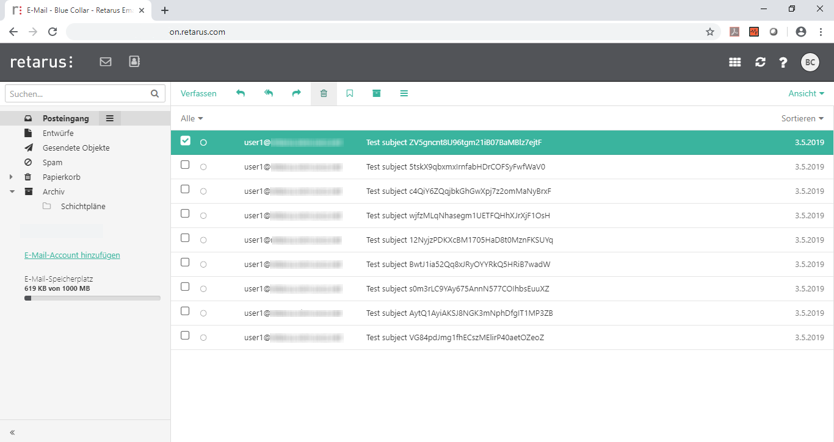
With Retarus Email Continuity your business and all employees stay productive, even if your own email infrastructure becomes unavailable. When designing the service, we consciously opted for a technology which is not based on Microsoft products. In this way, we can ensure that your business can continue operating, even in the case of these systems failing or coming under sustained and targeted attack.