A particularly nasty piece of malware is currently doing the rounds – with such devastating consequences that it even earned a report on Germany’s main newscast “Tagesschau”.
“Emotet”, as the malware has become known, has also succeeded in paralyzing entire company networks. The gateway for this cunningly programmed malware is email with an attached word document. The attachment contains dangerous macros which are also able to download additional malware. The emails look deceptively like genuine emails received from colleagues at the recipient’s own company.
The German Federal Office for Information Security (BSI) and the Alliance for Cyber Security recommend taking steps including the following in this regard: “Email servers should reject emails coming in from outside the organization bearing sender addresses belonging to the company’s own organization (no matter whether it’s in the envelope header, in the from-header or in the displayed name) and send them to quarantine, or at least mark them clearly in the subject line.”
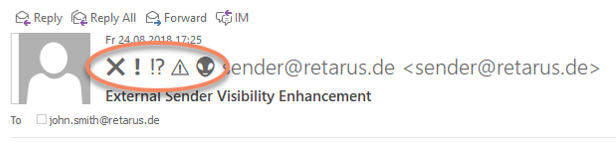
And the latter is exactly what Retarus E-Mail Security’s “External Sender Visibility Enhancements” (ESVE) function does. The feature has been a permanent component of the Essential Protection package since the end of August. This allows your email users to see at a glance whether an email with a sender ostensibly from within the company network has actually been received via an external relay.
Beyond that, we can only add our voice to the recommendations the BSI makes with regard to email security. We published a somewhat easier-to-use document on user education a while ago; the content is rather timeless and remains just as valid now as it was then.
You can find more information about Retarus E-Mail Security on our website or directly from your local Retarus representative.



